Proposed Solution: NetBird + Microsoft SSPR
What is NetBird?
Section titled “What is NetBird?”NetBird is an open-source, WireGuard-based mesh VPN (v0.66.4, 23,700+ GitHub stars, 131+ contributors, backed by the German Federal Ministry of Education and Research). Unlike traditional hub-and-spoke VPNs (like GlobalProtect), NetBird:
- Has no exposed login portal — there is no web page for attackers to spray credentials against. Authentication is delegated to Microsoft Entra ID via OIDC. WireGuard silently drops unauthorized connections.
- Uses WireGuard encryption — formally verified cryptography (ChaCha20-Poly1305, Curve25519). WireGuard’s codebase is ~4,000 lines vs. 100,000+ for IPsec implementations.
- Connects devices directly (peer-to-peer) — traffic does not funnel through a central bottleneck
- Runs as a background service — auto-connects at boot via setup key, no user interaction required
- Is 100% open source and can be fully self-hosted at no per-user cost (BSD-3 client, AGPLv3 server)
- Integrates with Microsoft Entra ID for SSO via OIDC, with JWT-based group sync
NetBird’s CVE history: Only 2 CVEs have ever been reported — both server-side management issues (default credentials in self-hosted installer, static IV in audit events DB). The WireGuard data plane has never been compromised.
Architecture
Section titled “Architecture”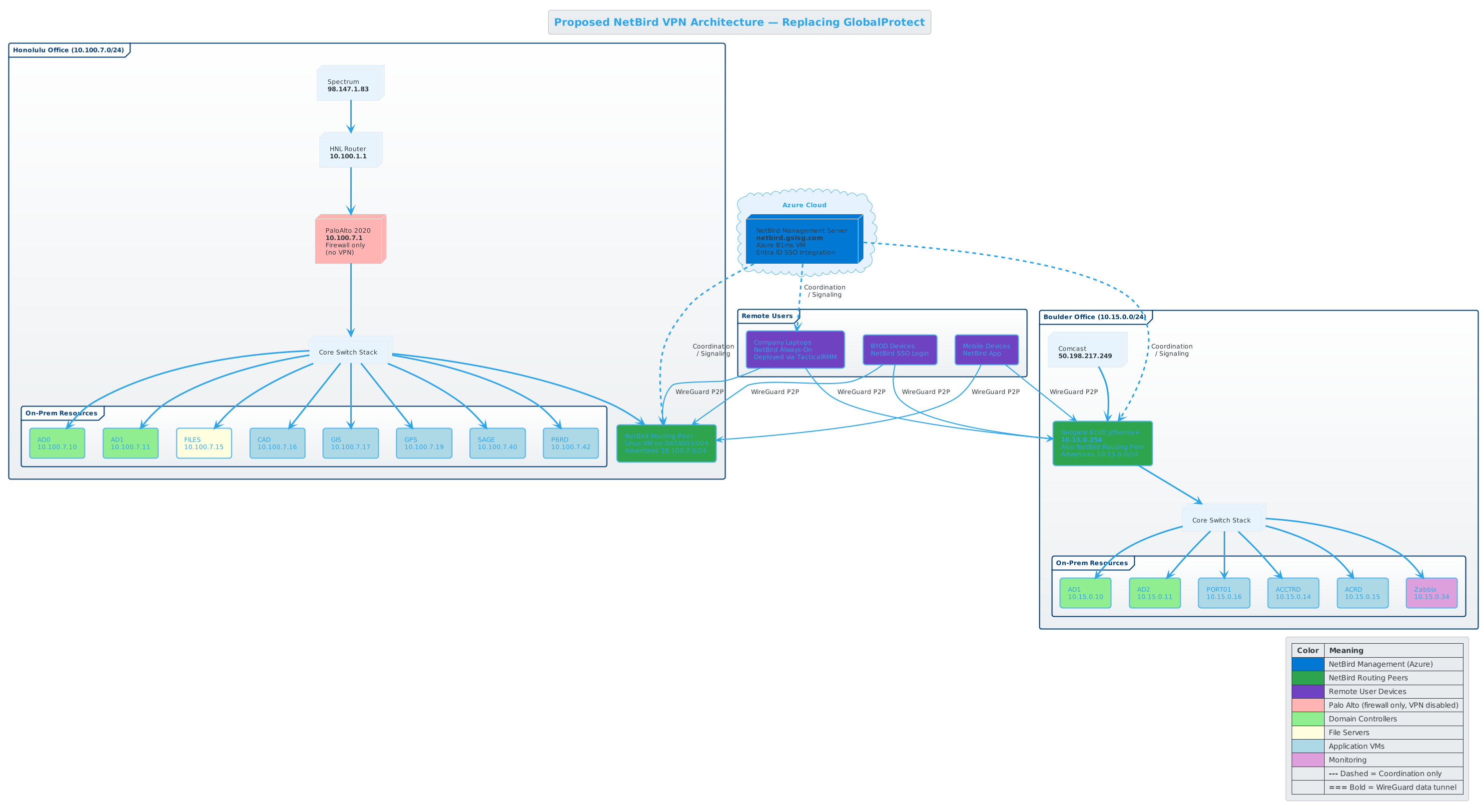
| Component | Specification | Location | Monthly Cost |
|---|---|---|---|
| NetBird Management Server | Hyper-V VM (2 vCPU, 4 GB RAM), Ubuntu 24.04 | Boulder, DATA001/DATA007 | $0 |
| Honolulu Routing Peer | Hyper-V VM (1 vCPU, 1 GB RAM) | Honolulu, DATA003/DATA004 | $0 |
| Boulder Routing Peer | NetBird on Netgate 6100 pfSense+ (Intel Atom C3558, AMD64) | Boulder, 10.15.0.254 | $0 |
| NetBird Software | Self-hosted Community Edition | On-prem | $0 |
| Public access | Port-forward TCP 80/443 + UDP 3478 through Netgate 6100 | Boulder, 50.198.217.249 | $0 |
| Total | $0/month |
Key architectural notes:
- Zero infrastructure cost. All components run on existing Hyper-V hosts and the existing Netgate 6100. No cloud VMs needed.
- The management server only handles coordination/signaling metadata. User data traffic flows peer-to-peer and never touches this server. Existing WireGuard tunnels survive management server outages.
- The Netgate 6100 uses an Intel Atom C3558 (AMD64) — official NetBird pfSense x86_64 packages install directly.
- Ingress to the management server is port-forwarded through the Netgate 6100 in Boulder. DNS (
netbird.gsisg.com) points to the Comcast business IP (50.198.217.249). - Embedded relay server handles NAT traversal. Estimated 5-15% of connections relay (mostly cellular/field workers).
- SQLite database is adequate for 100-150 peers.
How This Solves the Password Reset Problem
Section titled “How This Solves the Password Reset Problem”End-to-end technical chain:
| Step | What Happens | Detail |
|---|---|---|
| 1 | NetBird SYSTEM service is running | Started at boot via setup key. WireGuard tunnel UP to routing peer. DC is reachable (ports 88, 53, 389, etc.) |
| 2 | User opens browser | Goes to passwordreset.microsoftonline.com or clicks “Reset Password” on Windows login screen. Traffic to Microsoft cloud goes via normal internet (not tunnel). |
| 3 | MFA verification | User verifies identity via Authenticator app or phone |
| 4 | User enters new password | Entra ID encrypts with 2048-bit RSA + 256-bit AES-GCM, sends via HTTPS to tenant-specific Azure Service Bus relay |
| 5 | Entra Connect receives reset | On-prem Entra Connect decrypts, finds user via cloudAnchor attribute, calls AD DS SetPassword API. On-prem password policy enforced. |
| 6 | AD updated | New password is set in Active Directory. Replication propagates to other DCs (seconds to 15 min). |
| 7 | User locks workstation | Win+L |
| 8 | User unlocks with NEW password | Windows sends credential through NetBird tunnel to DC. Kerberos (port 88) validates, issues TGT. Cached credential hash updated. |
| 9 | Done | User is logged in with new password. All future logins use updated cached credentials. |
Required ports through the NetBird tunnel for AD functionality: DNS (53), Kerberos (88, 464), NTP (123), RPC (135), LDAP (389), SMB (445), LDAPS (636), Global Catalog (3268, 3269), RPC ephemeral (49152-65535)
SSPR licensing requirement: Entra ID P1 minimum — included at no extra cost in Microsoft 365 Business Premium ($22/user/mo) or M365 E3 ($36/user/mo).
End-User Experience
Section titled “End-User Experience”For general staff (90% of users): Nothing changes from their perspective.
- TacticalRMM deploys NetBird silently as a Windows service
- No application to open, no tray icon to click, no login prompt
- The service starts at boot and runs in the background
- Their machine silently has access to Domain Controllers at both sites
- When they need to reset their password, they go to
aka.ms/ssprin any browser - No “connecting to VPN” step — it’s already connected
For power users (10%): Same experience, plus resource access.
- Same silent background service
- SMB shares (mapped drives) work as if they’re in the office
- RDP to CAD/GIS/SAGE VMs works normally
- No manual VPN connect/disconnect cycle
For IT: Web-based management dashboard.
- Visual access control policies (no JSON editing)
- Group sync from Entra ID via JWT claims at login
- Activity monitoring and peer health
- REST API for integration with Zabbix or other monitoring